Last Updated On : 3-Mar-2026
Total 54 Questions
The smartest way to prepare for your Fortinet FCSS_SASE_AD-24 exam isn't just reading—it's practicing. Our FCSS - FortiSASE 24 Administrator practice test bridge gap, transforming your knowledge into a passing score. Familiarize yourself with the exact style and difficulty of the real Fortinet FCSS_SASE_AD-24 practice questions, so there are no surprises. Get detailed feedback to identify your strengths and target your weaknesses, making your study time more efficient.
During FortiSASE provisioning, how many security points of presence (POPs) need to be configured by the FortiSASE administrator?
A. 3
B. 4
C. 2
D. 1
Summary:
FortiSASE is a cloud-native service with a global network of Security PoPs. A key administrative task during initial setup is to define which of these PoPs will be responsible for inspecting and securing your organization's traffic. The configuration requires selecting a primary and a secondary PoP to ensure high availability and redundancy.
Correct Option:
C. 2
The FortiSASE administrator must configure a minimum of two Security PoPs: a Primary PoP and a Secondary (backup) PoP. This configuration provides automatic failover. If the Primary PoP becomes unreachable or experiences an issue, user sessions will automatically and seamlessly fail over to the Secondary PoP, ensuring continuous security and connectivity without manual intervention.
Incorrect Option:
A. 3:
While an administrator can configure more than two PoPs for geographic redundancy, it is not the mandatory minimum. The provisioning process requires at least one primary and one secondary.
B. 4:
Configuring four PoPs is possible for large or globally distributed organizations, but it is far beyond the required minimum and is not necessary for basic provisioning.
D. 1:
Configuring only a single PoP would create a single point of failure. If that one PoP becomes unavailable, all secured remote access would be lost. High availability, a core benefit of SASE, requires at least two.
Reference:
Fortinet Documentation Library: FortiSASE Administration Guide - Configuring Security PoPs
When viewing the daily summary report generated by FortiSASE. the administrator notices that the report contains very little data. What is a possible explanation for this almost empty report?
A. Digital experience monitoring is not configured.
B. Log allowed traffic is set to Security Events for all policies.
C. The web filter security profile is not set to Monitor
D. There are no security profile group applied to all policies.
Summary:
Daily summary reports in FortiSASE are generated from the logs of traffic that has passed through its security policies. If these reports are nearly empty, it indicates that logging for the vast majority of traffic is not enabled. The most common cause is a global logging setting that instructs the system only to record security incidents (like blocked connections or detected threats) and to ignore all traffic that was permitted.
Correct Option:
B. Log allowed traffic is set to Security Events for all policies.
This setting is the most direct explanation. When "Log Allowed Traffic" is configured as "Security Events," FortiSASE only generates a log entry when a security profile (such as Antivirus, IPS, or Web Filter) detects and blocks a threat. All other permitted traffic, which constitutes the majority of network activity, is not logged. Without these logs, the daily summary report has very little data to display, as it relies on log data to generate statistics and charts.
Incorrect Option:
A. Digital experience monitoring is not configured.
While DEM provides valuable performance metrics, its absence would not cause the main security summary report to be empty. The daily summary report is primarily based on security and traffic logs, not DEM synthetic tests.
C. The web filter security profile is not set to Monitor.
If the web filter is set to "Block" instead of "Monitor," it would still generate logs for the blocked connections. In fact, a "Block" action might generate more security event logs. The setting itself does not disable the logging of allowed web traffic; that is controlled by the global "Log Allowed Traffic" setting.
D. There are no security profile group applied to all policies.
While this is a poor security practice, it would not result in an empty report. Without security profiles, traffic would still be allowed and would be logged if the "Log Allowed Traffic" setting was enabled for "All Sessions." The lack of profiles would mean fewer security events, but the report would still show basic traffic data.
Reference:
Fortinet Documentation Library: FortiSASE Administration Guide - Logging and Reporting (This covers the log settings that directly feed into report generation).
A FortiSASE administrator is configuring a Secure Private Access (SPA) solution to share endpoint information with a corporate FortiGate.
Which three configuration actions will achieve this solution? (Choose three.)
A. Add the FortiGate IP address in the secure private access configuration on FortiSASE.
B. Use the FortiClient EMS cloud connector on the corporate FortiGate to connect to FortiSASE
C. Register FortiGate and FortiSASE under the same FortiCloud account.
D. Authorize the corporate FortiGate on FortiSASE as a ZTNA access proxy.
E. Apply the FortiSASE zero trust network access (ZTNA) license on the corporate FortiGate.
Summary:
This scenario describes integrating FortiSASE with an on-premises FortiGate for a unified Secure Private Access (SPA) and ZTNA solution. The goal is to allow the on-premises FortiGate to see the rich endpoint context (like ZTNA tags from FortiClient) collected by FortiSASE. This enables the FortiGate to make intelligent access decisions for users connecting to internal applications, creating a seamless hybrid security posture.
Correct Option:
A. Add the FortiGate IP address in the secure private access configuration on FortiSASE.
This is a necessary step to establish a trusted connection. The FortiSASE cloud must be explicitly configured to know the IP address of the on-premises FortiGate that it will be sharing endpoint information with. This defines the destination for the ZTNA tag data.
C. Register FortiGate and FortiSASE under the same FortiCloud account.
This is a foundational requirement for the integration. Sharing a common FortiCloud account provides a unified management and trust domain. It allows the two products to recognize each other as part of the same organization and securely exchange information.
D. Authorize the corporate FortiGate on FortiSASE as a ZTNA access proxy.
This action formally registers the on-premises FortiGate with FortiSASE in the specific role of a ZTNA Access Proxy. This tells FortiSASE, "Send the endpoint context information for my users to this specific FortiGate device so it can enforce ZTNA rules for accessing internal applications."
Incorrect Option:
B. Use the FortiClient EMS cloud connector on the corporate FortiGate to connect to FortiSASE
This is incorrect. The "EMS Cloud Connector" is a feature for connecting a FortiGate to a FortiClient EMS server, not to FortiSASE. The integration between FortiGate and FortiSASE is done natively through the FortiCloud account and the SPA/ZTP configuration, not via an EMS connector
E. Apply the FortiSASE zero trust network access (ZTNA) license on the corporate FortiGate.
This is incorrect and not a valid procedure. FortiSASE and FortiGate are licensed separately. A FortiSASE license cannot be applied to a physical FortiGate appliance. The FortiGate requires its own valid license and contract to enable ZTNA features.
Reference:
Fortinet Documentation Library: FortiSASE Administration Guide - Configuring Secure Private Access
Refer to the exhibits.
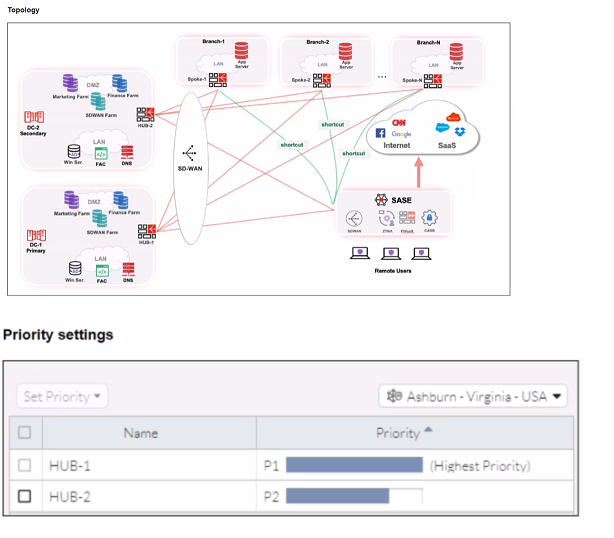
When remote users connected to FortiSASE require access to internal resources on
Branch-2. how will traffic be routed?
A. FortiSASE will use the SD-WAN capability and determine that traffic will be directed to HUB-2. which will then route traffic to Branch-2.
B. FortiSASE will use the AD VPN protocol and determine that traffic will be directed to Branch-2 directly, using a static route
C. FortiSASE will use the SD-WAN capability and determine that traffic will be directed to HUB-1, which will then route traffic to Branch-2.
D. FortiSASE will use the AD VPN protocol and determine that traffic will be directed to Branch-2 directly, using a dynamic route
Summary:
The exhibit shows the SD-WAN "Set Priority" table for the Ashburn location. HUB-1 is configured as the highest priority (P1) path. FortiSASE uses SD-WAN rules and performance metrics to make routing decisions. For traffic destined for internal resources, it will select the highest-priority available path to enter the corporate network, which in this case is via HUB-1. Once inside the corporate network, internal routing will direct the traffic to Branch-2.
Correct Option:
C. FortiSASE will use the SD-WAN capability and determine that traffic will be directed to HUB-1, which will then route traffic to Branch-2.
The SD-WAN rule explicitly defines HUB-1 as the highest priority (P1) path for the Ashburn location. FortiSASE's SD-WAN logic will direct all traffic destined for the internal corporate network through this preferred, high-priority tunnel. Once the traffic reaches HUB-1 (the central datacenter or hub), the internal network's routing protocols (like OSPF or BGP) will take over to deliver the traffic to the final destination at Branch-2.
Incorrect Option:
A. FortiSASE will use the SD-WAN capability and determine that traffic will be directed to HUB-2. which will then route traffic to Branch-2.
This is incorrect because HUB-2 is configured as a lower priority (P2) path. SD-WAN will only use HUB-2 if the P1 path (HUB-1) is down or experiencing performance degradation that violates its SLA.
B. FortiSASE will use the AD VPN protocol and determine that traffic will be directed to Branch-2 directly, using a static route
While AD-VPN can facilitate direct spoke-to-spoke tunnels, the exhibit only shows a priority-based SD-WAN rule between FortiSASE and the hubs (HUB-1 and HUB-2). There is no information indicating a direct AD-VPN tunnel is established between FortiSASE (the client) and Branch-2. The routing decision is based on the configured SD-WAN priority, not a static route.
D. FortiSASE will use the AD VPN protocol and determine that traffic will be directed to Branch-2 directly, using a dynamic route
Similar to option B, this is incorrect. The configuration shown is an SD-WAN priority rule, not an AD-VPN dynamic routing setup for a direct branch connection. The primary path is through HUB-1.
Reference:
Fortinet Documentation Library: FortiSASE Administration Guide - SD-WAN (This covers how priority-based SD-WAN rules steer traffic).
You are designing a new network for Company X and one of the new cybersecurity policy requirements is that all remote user endpoints must always be connected and protected.Which FortiSASE component facilitates this always-on security measure?
A. site-based deployment
B. thin-branch SASE extension
C. unified FortiClient
D. inline-CASB
Summary:
The requirement for "always-on" protection means the security enforcement must be active before a user logs into their device and must persist regardless of network location (on-premises, public Wi-Fi, home). This requires a persistent security agent on the endpoint itself that can maintain a continuous connection to the FortiSASE cloud for policy enforcement, which is the core function of the unified FortiClient agent.
Correct Option:
C. unified FortiClient
The unified FortiClient agent is the component that facilitates always-on security. It can be configured to start automatically with the operating system, establishing a connection to FortiSASE before user login. It runs continuously in the background, ensuring that all network traffic from the endpoint is routed through FortiSASE's security stack for inspection and policy enforcement, regardless of the user's physical location or network connection.
Incorrect Option:
A. site-based deployment
This refers to extending SASE security to a physical branch office location using a device like a FortiGate. It does not provide direct, always-on protection for individual remote user endpoints, which is the focus of the question.
B. thin-branch SASE extension
This is a specific type of site-based deployment for small offices. Like option A, it secures a location's entire network traffic but is not the mechanism for ensuring individual, roaming endpoints are always protected.
D. inline-CASB
Inline-CASB is a security feature that provides deep visibility and control for SaaS application traffic. It is a component within the FortiSASE cloud that inspects traffic, but it is not the endpoint component that facilitates the "always-on" connection. The agent (FortiClient) is what brings the traffic to the inline-CASB.
Reference:
Fortinet Documentation Library: FortiSASE Solution Guide - Unified Agent (This covers the FortiClient agent's role in providing continuous security).
Which two components are part of onboarding a secure web gateway (SWG) endpoint?
(Choose two)
A. FortiSASE CA certificate
B. proxy auto-configuration (PAC) file
C. FortiSASE invitation code
D. FortiClient installer
Summary:
Onboarding an endpoint for Secure Web Gateway (SWG) involves configuring the device to route its web traffic through the FortiSASE cloud for security inspection. This can be achieved through two primary methods: manually configuring the device's proxy settings using a PAC file, or deploying the FortiClient agent which automatically handles the traffic steering and provides additional security features.
Correct Option:
B. proxy auto-configuration (PAC) file
A PAC file is a JavaScript file that instructs a web browser on when to use a proxy server. For clientless SWG access, the administrator provides this file to users. The browser uses the PAC file to automatically determine that traffic destined for the internet should be sent to the FortiSASE SWG proxy, while internal traffic can be sent directly.
D. FortiClient installer
The FortiClient installer is used for agent-based SWG deployment. When installed and configured with the FortiSASE connection details, FortiClient automatically routes all web traffic from the endpoint through the FortiSASE cloud. This method is more seamless for the user and provides a persistent, always-on connection.
Incorrect Option:
A. FortiSASE CA certificate
While the FortiSASE CA certificate is critically important for SSL inspection to function without causing certificate warnings in the browser, it is not a component used to onboard the endpoint. It is a prerequisite for deep inspection after the traffic is already being routed to FortiSASE.
C. FortiSASE invitation code
An invitation code is used for onboarding users and endpoints specifically for Zero Trust Network Access (ZTNA) to specific applications. It is not the mechanism used for general Secure Web Gateway (SWG) onboarding, which relies on a PAC file or the FortiClient agent for traffic steering.
Reference:
Fortinet Documentation Library: FortiSASE Administration Guide - Onboarding Endpoints (This covers both the PAC file and FortiClient methods for directing traffic to FortiSASE).
Refer to the exhibit.

In the user connection monitor, the FortiSASE administrator notices the user name is showing random characters. Which configuration change must the administrator make to get proper user information?
A. Turn off log anonymization on FortiSASE.
B. Add more endpoint licenses on FortiSASE.
C. Configure the username using FortiSASE naming convention.
D. Change the deployment type from SWG to VPN.
Summary:
The exhibit shows a user connection monitor where the username is displayed as a string of random characters ("Pstb6450a1975af"). This is a classic symptom of log anonymization being enabled. This security feature is designed to protect user privacy in logs by replacing actual usernames with pseudonyms or hashes, which prevents an administrator from identifying the specific user associated with a session.
Correct Option:
A. Turn off log anonymization on FortiSASE.
The random character string is a pseudonym generated by the log anonymization feature. To display the actual, readable usernames in the connection monitor and logs, the administrator must disable this feature in the FortiSASE global settings. This will stop the system from obfuscating user identities and will allow real names to appear for monitoring and troubleshooting purposes.
Incorrect Option:
B. Add more endpoint licenses on FortiSASE.
A lack of licenses would prevent users from connecting altogether or would be indicated by a license violation warning. It has no bearing on how usernames are displayed in the logs once a user is connected.
C. Configure the username using FortiSASE naming convention.
Usernames are typically defined in the identity provider (like Active Directory or Azure AD) that FortiSASE integrates with. FortiSASE does not impose its own naming convention that would cause a username to appear as a random hash if not followed. The obfuscation is a direct result of an anonymization setting.
D. Change the deployment type from SWG to VPN.
The deployment type (SWG or VPN) determines how users connect and what resources they access, but it does not control the fundamental logging format for usernames. The log anonymization feature applies globally across all deployment types within FortiSASE.
Reference:
Fortinet Documentation Library: FortiSASE Administration Guide - Log Anonymization (This document explains the feature that masks user identities in logs).
| Page 1 out of 8 Pages |
| 1234 |
Choosing the right preparation material is critical for passing the FCSS - FortiSASE 24 Administrator exam. Here’s how our FCSS_SASE_AD-24 practice test is designed to bridge the gap between knowledge and a passing score.