Last Updated On : 25-May-2026
Total 68 Questions
Refer to the exhibit.
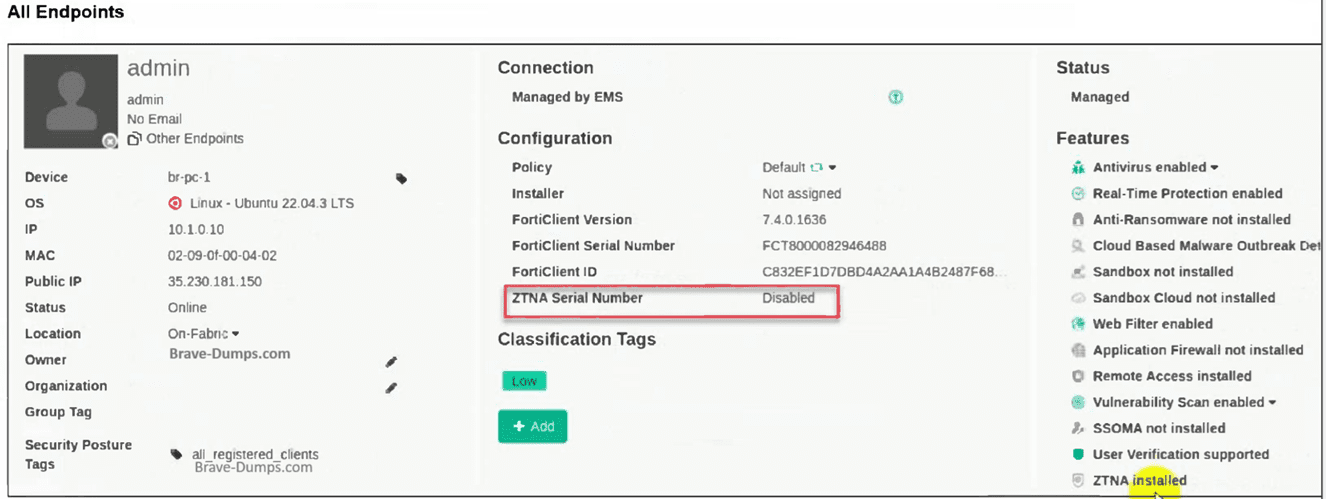
The zero trust network access (ZTNA) serial number on endpoint br-pc-1 is in a disabled
state.
What is causing the problem? (Choose one answer)
A. The ZTNA feature is not installed on FortiClient.
B. The ZTNA destinations endpoint profile is disabled.
C. The ZTNA is disabled due to FortiClient disconnected from FortiClient EMS.
D. The ZTNA certificate has been revoked by administrator.
Explanation:
This question checks the reason behind the ZTNA Serial Number appearing as “Disabled” in the FortiClient EMS endpoint details pane for a managed Linux device. It evaluates knowledge of ZTNA certificate lifecycle and the strict dependency on active, ongoing connectivity between the FortiClient endpoint and EMS in version 7.4.
✅ Correct Option:
C. The ZTNA is disabled due to FortiClient disconnected from FortiClient EMS.
When FortiClient loses connection to EMS, the endpoint can no longer maintain its managed state. As a result, EMS marks the ZTNA feature status as Disabled and the ZTNA Serial Number field shows “Disabled” because the certificate cannot be kept active or refreshed without continuous EMS management. This matches the exhibit behavior exactly.
❌ Incorrect options:
A. The ZTNA feature is not installed on FortiClient.
This option is wrong because the Features section in the exhibit clearly lists “ZTNA installed” at the bottom, confirming that the ZTNA module is already present and was successfully installed on this endpoint.
B. The ZTNA destinations endpoint profile is disabled.
This option does not fit because a disabled ZTNA Destinations profile would prevent initial certificate provisioning and ZTNA feature activation. Since the exhibit already shows ZTNA as installed, the profile must have been enabled at some point and the current “Disabled” status is not caused by the profile itself.
D. The ZTNA certificate has been revoked by administrator.
This option is incorrect since certificate revocation by an administrator would typically cause authentication failures, connection errors, or an “Invalid” certificate state rather than simply displaying the ZTNA Serial Number field as “Disabled” in the EMS console.
Reference:
⇒ Prepare FortiClient and FortiClient EMS for ZTNA – FortiGate / FortiOS 7.4.0
Confirms that ZTNA certificate provisioning and the display of a valid ZTNA Serial Number require the endpoint to remain connected to EMS; disconnection causes the feature to revert to Disabled status.
⇒ Endpoint profile – FortiClient EMS 7.4.0 Administration Guide
Explains that ZTNA-related settings (including certificate handling) depend on active management by EMS and that loss of connectivity affects feature status visibility in the All Endpoints view.
Which three types of antivirus scans are available on FortiClient? (Choose three )
A. Proxy scan
B. Full scan
C. Custom scan
D. Flow scan
E. Quick scan
Explanation:
This question tests knowledge of FortiClient's on-demand antivirus scan types available in the EMS 7.4 Administrator context. It evaluates understanding of endpoint protection features for scheduled or manual scans targeting rootkits, system files, and specific locations.
✅Correct Option:
B. Full scan:
Performs comprehensive rootkit detection first, then scans all files, executables, DLLs, drivers, and system areas across the entire endpoint filesystem. This ensures maximum threat coverage including boot sectors and hidden malware that lighter scans might miss. Ideal for thorough periodic maintenance.
C. Custom scan:
Starts with rootkit detection, then allows administrators or users to select specific files, folders, or drives for targeted scanning. This provides precise control for investigating suspicious areas without unnecessary full-system overhead, balancing efficiency and focus.
E. Quick scan:
Begins with rootkit detection and focuses solely on running executables, DLLs, drivers, and critical system components. Designed for fast threat checks on active processes without scanning the entire disk, making it suitable for frequent, low-impact security verifications.
❌Incorrect options:
A. Proxy scan:
Not available in FortiClient antivirus features.
Proxy scanning is specific to FortiGate web proxy functionality for inspecting HTTP/HTTPS traffic.
It operates at the network gateway level, not endpoint AV scanning.
D. Flow scan:
Not a FortiClient endpoint scan type option.
Flow-based scanning is used by FortiGate for real-time network traffic analysis on interfaces.
It performs inline inspection without file storage, unlike on-demand endpoint scans.
Reference:
🔧 FortiClient EMS AntiVirus Protection - Confirms Quick, Full, and Custom as standard AV scan types with rootkit detection.
FortiClient EMS endpoint policies
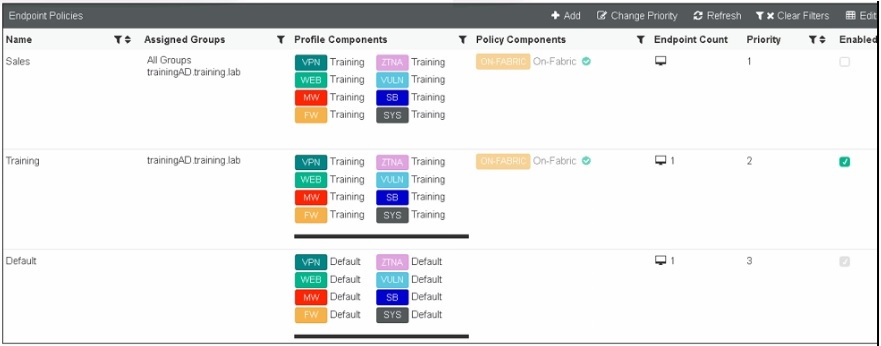
Refer to the exhibit, which shows multiple endpoint policies on FortiClient EMS. Which
policy is applied to the endpoint in the AD group trainingAD.
A. The Training policy
B. Both the Sales and Training policies because their priority is higher than the Default policy
C. The Default policy because it has the highest priority
D. The sales policy
Explanation:
This question tests your understanding of how FortiClient EMS applies endpoint policies based on AD group membership and policy priority. You must analyze the exhibit to determine which policy is applied to an endpoint belonging to the AD group "trainingAD".
✅Correct Option:
✅ A. The Training policy
The endpoint in the AD group "trainingAD" matches the "Assigned Groups" column of the Training policy, which shows "trainingAD_training_lab". Since the endpoint belongs to this AD group, the Training policy is applied, regardless of the Default policy's higher priority (priority 3 vs. priority 2).
❌Incorrect options:
❌ B. Both the Sales and Training policies because their priority is higher than the Default policy
Policies are not combined or cumulative. Only one policy applies to an endpoint at a time based on group matching, and the Sales policy is assigned to "All Groups" which would include this endpoint, but the Training policy takes precedence because it is a specific match.
❌ C. The Default policy because it has the highest priority
Priority determines order when multiple policies match an endpoint, but the Default policy is only applied when no other policy matches the endpoint's group. Since the endpoint matches the Training policy's assigned group, Default does not apply.
❌ D. The Sales policy
Although the Sales policy is assigned to "All Groups" (which includes trainingAD), FortiClient EMS applies the most specific policy match. The Training policy explicitly lists trainingAD as an assigned group, making it a more specific match than the broad "All Groups" assignment.
Reference:
⇒ Fortinet Documentation: FortiClient EMS 7.4 Administration Guide - Endpoint Policies
This confirms that policies are assigned based on group membership, and when multiple policies match, the system uses the most specific assignment rather than combining policies.
Refer to the exhibit.
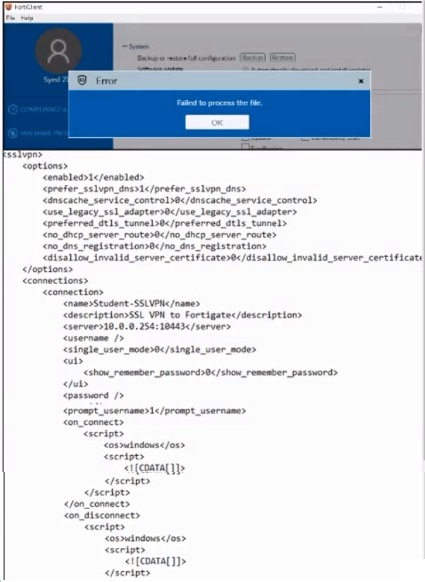
An administrator has restored the modified XML configuration file to FortiClient and sees
the error shown in the exhibit.
Based on the XML settings shown in the exhibit, what must the administrator do to resolve
the issue with the XML configuration file?
A. The administrator must resolve the XML syntax error.
B. The administrator must use a password to decrypt the file
C. The administrator must change the file size
D. The administrator must save the file as FortiClient-config conf.
Explanation:
The question presents an error message "Failed to process the file" when restoring an XML configuration to FortiClient, along with a partial XML file. The core issue lies in the malformed XML structure visible in the provided snippet.
✅Correct Option:
The XML configuration snippet shows an unclosed ksslvpn tag at the beginning and an unclosed disallow_invalid_server_certificate tag within the options. These are clear XML syntax errors that prevent the file from being parsed correctly by FortiClient, leading to the "Failed to process the file" error.
❌Incorrect options:
B. The administrator must use a password to decrypt the file.
This is incorrect because the error shown is related to file processing due to syntax issues, not encryption. XML configuration files are typically handled as plain text by FortiClient for parsing, and a decryption password is not relevant here.
C. The administrator must change the file size.
This is incorrect. The file size itself is not the cause of a "Failed to process the file" error. The problem lies with the invalid content and structure of the XML within the file, which prevents FortiClient from reading it correctly.
D. The administrator must save the file as FortiClient-config.conf.
This is incorrect. While proper naming conventions are important, the displayed error explicitly points to a processing failure, which is a content-related issue (syntax error in XML) rather than an incorrect file name or extension.
Reference:
⇒ Fortinet FortiClient XML Configuration Guide [docs.fortinet.com] This guide confirms the proper XML structure and syntax required for FortiClient configuration files, highlighting the importance of correctly closed tags and well-formed XML to avoid processing errors.
An administrator is required to maintain a software vulnerability on the endpoints, without showing the feature on the FortiClient. What must the administrator do to achieve this requirement?
A. Select the vulnerability scan feature in the deployment package, but disable the feature on the endpoint profile
B. Disable select the vulnerability scan feature in the deployment package
C. Click the hide icon on the vulnerability scan profile assigned to endpoint
D. Use the default endpoint profile
Explanation:
This question tests your understanding of how FortiClient EMS manages features on endpoints while controlling visibility. The goal is to maintain a software vulnerability feature on endpoints without showing it in the FortiClient interface.
✅ Correct Option: A
Selecting the vulnerability scan feature in the deployment package ensures EMS can manage and update the functionality on endpoints. Disabling it in the endpoint profile hides the feature from the FortiClient console, allowing centralized control while keeping it hidden from end users.
❌ Incorrect options:
B. Disable select the vulnerability scan feature in the deployment package:
Disabling the feature in the deployment package removes it completely from EMS management. This prevents the administrator from maintaining the vulnerability scan on the endpoints, which fails to meet the requirement of keeping the feature active but hidden.
C. Click the hide icon on the vulnerability scan profile assigned to endpoint:
FortiClient EMS does not provide a “hide icon” for feature profiles. Attempting this would not hide the feature from the FortiClient interface, so it does not achieve the requirement.
D. Use the default endpoint profile:
The default endpoint profile does not hide or disable the vulnerability scan feature. Assigning this profile would leave the feature visible to end users, which conflicts with the requirement to conceal it.
Reference:
⇒ FortiClient EMS Administration Guide
– Confirms how features can be deployed and hidden using endpoint profiles.
Refer to the exhibit.

Based on the settings shown in the exhibit, which action will FortiClient take when users try
to access www facebook com?
A. FortiClient will allow access to Facebook.
B. FortiClient will block access to Facebook and its subdomains.
C. FortiClient will monitor only the user's web access to the Facebook website
D. FortiClient will prompt a warning message to want the user before they can access the Facebook website
Explanation:
This question tests your understanding of FortiClient web filter exclusions and how URL filtering rules are applied. The exhibit shows a web filter exclusion configuration that specifically defines how Facebook should be handled.
✅Correct Option:
✅ A. FortiClient will allow access to Facebook.
The exhibit shows a Web Filter Exclusion configured with URL "facebook.com" and Action set to "Allow". This exclusion overrides any category-based filtering that might otherwise apply to Facebook. Since Facebook typically falls under "Social Networking" category, this explicit allow rule permits access regardless of how that category is configured.
❌Incorrect options:
❌ B. FortiClient will block access to Facebook and its subdomains.
The exclusion is configured with "Allow" action, not block. While wildcard type would cover subdomains, the action determines the result - allow in this case, not block.
❌ C. FortiClient will monitor only the user's web access to the Facebook website.
The exhibit shows a Web Filter Exclusion with Allow action, not a monitoring configuration. Monitoring would require different settings in the web filter profile.
❌ D. FortiClient will prompt a warning message to warn the user before they can access the Facebook website.
The exclusion is set to Allow, which grants access without warnings. Warning prompts would require a different action type such as "Warn" or "Authenticate" in the exclusion configuration.
Reference:
⇒ Fortinet Documentation: FortiClient 7.4 Administration Guide - Web Filter Exclusions
This confirms that web filter exclusions take precedence over category-based filtering, and the Action setting determines whether access is allowed, blocked, or monitored.
An administrator has a requirement to add user authentication to the ZTNA access for remote or off-fabric users Which FortiGate feature is required m addition to ZTNA?
A. FortiGate FSSO
B. FortiGate certificates
C. FortiGate explicit proxy
D. FortiGate endpoint control
Explanation:
This question tests your understanding of how user authentication is enforced for ZTNA access when users are working remotely or off-fabric. Standard ZTNA handles device identity via certificates, but adding user-level authentication requires an additional FortiGate feature to intercept and authenticate traffic before granting access.
✅ Correct Option:
C. FortiGate Explicit Proxy
FortiGate's Explicit Proxy is required to enforce user authentication on top of ZTNA for off-fabric/remote users. It acts as an intermediary that challenges users for credentials before allowing access, enabling identity-based policy enforcement alongside the existing device-based ZTNA certificate verification.
❌ Incorrect Options:
A. FortiGate FSSO
FSSO (Fortinet Single Sign-On) is used to passively collect domain login events from Active Directory environments. It is not designed to actively enforce authentication challenges for remote ZTNA users operating outside the corporate network.
B. FortiGate Certificates
Certificates are already a core component of ZTNA itself, used for device identity verification. They do not add a separate user authentication layer on top of existing ZTNA access control for remote users.
D. FortiGate Endpoint Control
Endpoint Control is used for managing FortiClient registrations and enforcing compliance posture checks. It does not provide the user authentication capability required for ZTNA access in off-fabric scenarios.
Reference:
🔧 Fortinet Docs – ZTNA User Authentication with Explicit Proxy
⇒ Confirms that FortiGate Explicit Proxy is required when adding user authentication to ZTNA access rules for remote and off-fabric users.
🔧 Fortinet ZTNA Architecture Guide – Off-Fabric Access
⇒ Explains the difference between device-based ZTNA verification and the additional user-identity layer enabled through explicit proxy configuration.
| Page 3 out of 10 Pages |
| 12345 |
| FCP_FCT_AD-7.4 Practice Test Home |
Choosing the right preparation material is critical for passing the Fortinet NSE 6 FortiClient EMS 7.4 Administrator exam. Here’s how our FCP_FCT_AD-7.4 practice test is designed to bridge the gap between knowledge and a passing score.